DDoS attacks do great harm to enterprise information systems or applications, may cause direct economic losses and brand damage, lead to business anomalies and the decline of user experience, cause the loss of data center customers, and form a serious security threat to the internal network
Threats to the security of network services or user business systems. Most enterprises have weak security awareness, lack of security protection and skills, network services are frequently subjected to malicious scanning and violent cracking, nearly half of the network services have security loopholes, and the security situation of network services is not optimistic.
Frequent internal and external data leakage events, hacker attacks or viruses increasingly industrialized, the lack of audit mechanism for key business processes of enterprise sensitive information, and the lack of database sensitive information protection technology will all lead to data leakage, so it is necessary to eliminate security vulnerabilities from data management.
The most dangerous threat to the system platform is the embedded threat in the system software or hardware chip, such as "Trojan horse" and "trap gate", and the "mechanism" set in a system or a component, which allows violation of security policy when specific data is input.
According to the needs of security level and operation and maintenance management, e Cloud divides and isolates the network area of the cloud platform, and provides multi-layer security isolation, access control, border security and other comprehensive network security for the carrying network of the cloud platform.
e Cloud has complete procedures, specifications, systems and strategies for handling security incidents. According to the urgency and severity of security incidents, three differentiated emergency response services have been developed: Critical (7 X 24), Serious (7 X 8), and Important (5 X 8), a professional security service team is also equipped to provide users with comprehensive security services
e Cloud monitors and protects cloud boundaries from multiple levels and angles: using professional Anti-DDos equipment to provide more refined DDos protection capabilities, and jointly build the first line of defense for boundary security. Border firewall, IPS, and cloud WAF respectively provide network layer access control, four to seven layers of intrusion detection and defense, and provide professional-level Web security protection capabilities.
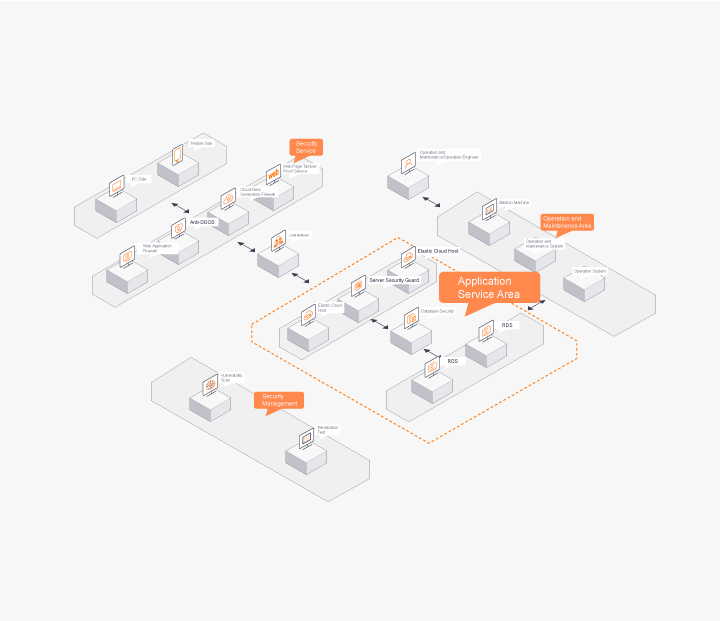
Cloud Platform Data Security as the Core e Cloud general scene security service solution, which takes cloud platform data security as the core, mainly covers the basic fields of network, system, application, service, operation and maintenance. Complete Security Service System Covers network, system, application, service, operation and maintenance. Services include cloud-network linkage, end-side security, boundary security, automatic evaluation, and expert services.
 Contact Us
Contact Us
We use cookies to ensure your high-speed browsing experience. By continuing to browse this site, you agree to our use of cookies. Details


